
Overview
Palo Alto Networks Unit 42 threat research team has just uncovered a new set of attacks by the Sofacy group using malicious emails targeting foreign affairs agencies and ministries in North America and Europe, including a European embassy in Moscow.
Given the significant activity attributed to Sofacy, and the new evidence directly targeting the diplomatic community, Palo Alto Networks wants to ensure that foreign affairs agencies around the world understand how the attacks are carried out, and what agencies and personnel can do to protect themselves.
The Sofacy Group (AKA APT28, Grizzly Steppe, Fancy Bear, STRONTIUM, Sednit, Tsar Team, Pawn Storm) is a well-known hacking organization widely reported to be associated with Russia by the US Intelligence Community, numerous media reports and other cybersecurity companies. Sofacy Group has been associated with many attacks against targets around the world, including the International Olympic Committee (IOC) in 2018, the World Anti-Doping Agency in 2016, the Dutch Safety Board in 2015, and German, French, Ukrainian, and Dutch political and military targets throughout 2014 through 2018.
How the Attacks are Carried Out: Via Email
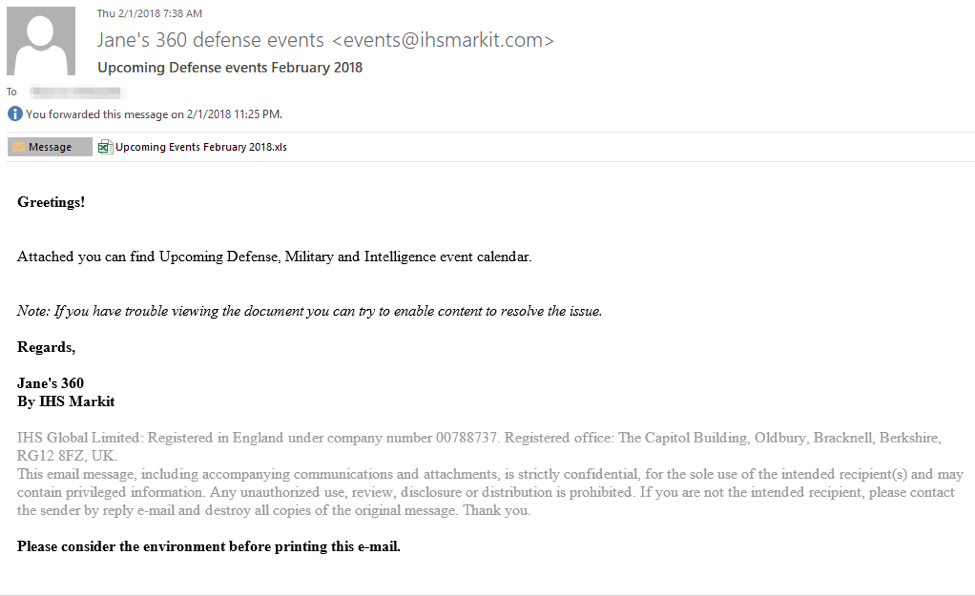
These attacks begin with an email sent to a carefully chosen target in the agency. The recent spoofed emails we have seen are forged to appear to come from Jane’s 360 Defense Events to tell the recipient about events coming up in 2018.
- The actual subject line is “Upcoming Defense events February 2018”
- The sender address falsely claims to be “Jane's 360 defense events <events@ihsmarkit.com>"
- The email has a Microsoft Excel spreadsheet attached and urges the recipient to open the attachment Most importantly, the email says “If you have trouble viewing the document you can try to enable content to resolve the issue”
The figure below shows an example.
Once the recipient opens the Excel spreadsheet, she or he does have trouble viewing the document: it opens as a blank spreadsheet. The attackers are relying on the recipient to follow the instruction in the email and click “Enable Content”. You can see below what the spreadsheet looks like and the enable content button.
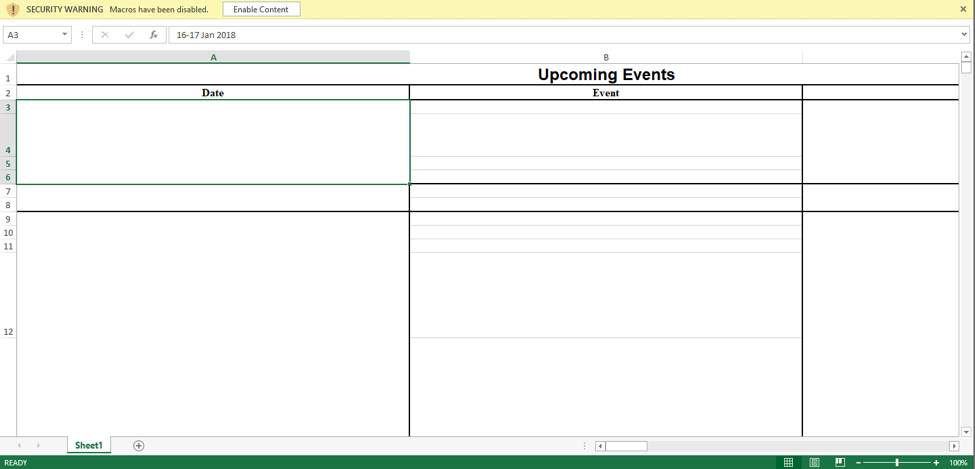
Clicking the “Enable Content” button is the key to the attack. While it makes the text in the spreadsheet visible and so seems to solve the problem, it’s a trick: It’s really running a program that silently installs a program on the system. This program gives the attackers complete control over the computer and can enable them to copy documents, usernames, passwords, account information and even take screenshots.
How you can protect yourself
There are several things that you can do to help protect against these latest Sofacy attacks and others like it. With the public awareness of this particular decoy, it is highly likely that the Sofacy group will shift their attacks to spoof emails from a different organization to continue carrying out these attacks. Additionally, this attack technique is not exclusive to the Sofacy Group.
Therefore, these suggested actions can protect not just against these known attacks but others like it.
- First: Ensure your agency is running advanced security that can provide protection against attacks like this.
- Second: You may also want to work with your security team to determine if you received this particular email and if this attack potentially impacted you.
- Third: Be cautious when opening attachments that you get through email. If you get an unexpected email with an attachment be very wary.
- Fourth: Be even more cautious when opening an attachment that in some way tells you to “Enable Content”. The “Enable Content” button is actually a security protection in Microsoft Word and Excel: it prevents programs from running. Attackers regularly try to get people to turn off this protection using tricks like we see here.
An unexpected email message with an attachment that says you should “enable content” has a high likelihood of being malicious in some way. If you get an email like this, you shouldn’t open the attachment and click “enable content”. Instead, you should verify that the message and the attachment are legitimate by contacting the sender in some way other than replying to the email (because replying to the email may go back to the attackers who will, of course, say it’s legitimate). Or, just delete the message and report it to your security team.
Palo Alto Networks Unit 42 regularly researches threats like these and provides information about them on our blog.
Get updates from
Palo Alto
Networks!
Sign up to receive the latest news, cyber threat intelligence and research from us
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement.
