Dridex, the latest descendent of the Bugat/Feodo/Cridex banking Trojan lineage has been a constant source of attacks using the malware since its release in July. To date, Dridex has centered on sending executable attachments via e-mail. That seems to have changed this week, as we’ve seen a tactical shift to sending those executable attachments via Microsoft Word documents loaded with macros that download and execute the malware.
Like its precursors, Dridex is a sophisticated Banking Trojan, similar to the infamous Zeus malware. Its core functionality is to steal credentials of online banking websites and allow a criminal to use those credentials to initiate transfers and steal funds. Dridex uses an XML-based configuration file to specify which websites it should target and other options for the malware. For instance, the configuration specifies which websites to capture form submissions from, and which to ignore with the following XML.
<formgrabber>
<url type="deny">\.(swf)($|\?)</url>
<url type="deny">/isapi/ocget.dll</url>
<url type="allow">^https?://aol.com/.*/login/</url>
<url type="allow">^https?://accounts.google.com/ServiceLoginAuth</url>
<url type="allow">^https?://login.yahoo.com/</url>
<url type="allow">^https?://login.live.com/</url>
<url type="deny">^https?://(\w+\.)?aol.com</url>
<url type="deny">^https?://(\w+\.)?facebook.com/</url>
<url type="deny">^https?://(\w+\.)?google</url>
<url type="deny">^https?://(\w+\.)?yahoo</url>
<url type="deny">^https?://(\w+\.)?youtube.com</url>
<url type="deny">^https?://(\w+\.)?live.com</url>
<url type="deny">^https?://(\w+\.)?twitter.com</url>
<url type="deny">^https?://(\w+\.)?vk.com</url>
<url type="deny">^https.*ocsp\..+$</url>
<url type="deny">^https.*safebrowsing\..+$</url>
<url type="deny">^https?://fhr\.data\.mozilla\.com</url>
<url type="deny">^https://s.*\.symcd\.com</url>
<url type="deny">^https://s.*\.symcb\.com</url>
<url type="deny">^https.*ocsp2\..+$</url>
<url type="deny">localhost.+skypectoc/.+$</url>
<url type="deny">\.messenger\.live\.com</url>
<url type="deny">pipe\.skype\.com</url>
<url type="deny">\.optimatic\.com</url>
<url type="deny">hiro\.tv</url>
<url type="deny">spotxchange\.com</url>
<url type="deny">nielsen\.com</url>
<url type="deny">mapquest\.com</url>
<url type="deny">^https://.+\.skype\.com/api/</url>
<url type="deny">(//|\.)lphbs.com</url>
<url type="deny">(//|\.)zynga.com</url>
</formgrabber>
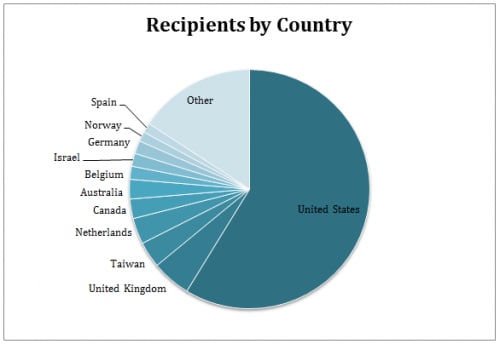
The first wave of this attack began on October 21, with e-mails claiming to carry invoices from Humber Merchant’s group. On October 22 and 23 (and today) we’ve seen new brands abused but the e-mails continued to use invoice themes. The organizations we’ve seen receiving these files break down into the following countries.
With this latest wave, WildFire has detected nine distinct Word documents, each of which uses the same technique to install Dridex. The word documents contain a complex VBA macro that downloads an executable from one of the following URLs and executes it on the system.
- http://gpsbah[.]com/images/1.exe
- http://jvsfiles[.]com/common/1.exe
- http://jvssys[.]com/js/1.exe
- http://mirafarm[.]ro/html/js/bin.exe
- http://palitosdepan[.]com/js/bin.exe
- http://www.juglarsa.com[.]ar/images/1.exe
These are all legitimate websites that appear to be compromised by the actors running this Dridex campaign. The files are each different versions of the Dridex malware that communicate with their command and control servers over HTTP. Kimberly from StopMalvertising has a great article on how this communication process works and allows Dridex to download its main criminal components.
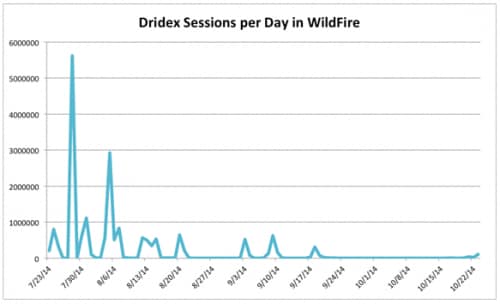
While the latest attack began this week, Dridex has been in the wild since late July, and since then our WildFire system has been detecting Dridex variants very effectively. As a result, we pulled data on all of the malware we’ve seen talking to known Dridex command and control servers to get an idea of the volume of Dridex activity since its release. Abuse.ch operates the Feodo Tracker, which tracks these servers and those used by earlier versions of the Trojan.
While the latest attacks are certainly significant, the volume we’ve observed has been much lower than in July and August when the first variants of Dridex were first observed.
You can protect yourself against this wave of Dridex attacks by disabling macros in Microsoft Word. Macro-based malware has been around for over well over a decade. Most organizations should have them disabled by default, enabling macros only for trusted files.
Get updates from
Palo Alto
Networks!
Sign up to receive the latest news, cyber threat intelligence and research from us
By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement.